Cloudflare: Mod_Cloudflare & How It Works
When you acquire the Cloudflare service, searching through your server access logs for information will be a bit different because of the way that the Cloudflare system interacts with the website traffic.
Because the Cloudflare service acts as a proxy, the access logs in the hosting environment will display the information of each site access as coming from Cloudflare. While this information is not “inaccurate,” it is partial.
This is where the Mod_Cloudflare module comes in to play.
Mod_Cloudflare is a module that allows the hosting web server to parse the *“CF-Connecting-IP” header. This HTTP header contains information of the original visitor’s IP address. This means that logging and protective server services will be able to effectively accomplish their tasks.
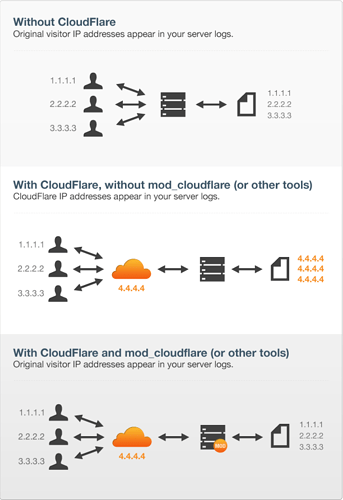
Please see the image and paragraphs below for a better understanding and breakdown of how the Mod_Cloudflare module interacts with the website traffic:
Image Source: Cloudflare.com
Without Cloudflare
In the first section of the image, you can see that the incoming traffic requests are being routed directly to the web server. With this configuration, the web server is accurately able to log the visitor’s IP addresses, as the traffic requests are not being routed to the Cloudflare system.
With Cloudflare, But Without Mod_Cloudflare Installed
In the second section, you can see that the incoming traffic requests are being routed to the Cloudflare service. These requests are then sent from the Cloudflare service to the web server to retrieve website content. When this action occurs, the web server, without the Mod_Cloudflare module installed, sees the request as the Cloudflare IP (represented by the IP address 4.4.4.4). In turn, the web server then logs the IP address 4.4.4.4 to the log files. This would also mean that the webserver’s protective services may think that an influx of traffic from 4.4.4.4 could be malicious and try to block it.
With Cloudflare and Mod_Cloudflare Installed
In the third section, you can see that the incoming traffic requests (represented by the IP address: 1.1.1.1, 2.2.2.2, 3.3.3.3) are routed to the Cloudflare system. From the Cloudflare service, requests are made from the web server. With the Mod_Cloudflare module enabled, the web server is able to determine who is actually requesting the content through the Cloudflare service and is then able to log the visitor’s IP addresses as they were when being directed to the Cloudflare service. Those visitors are logged by their representative IP address: 1.1.1.1, 2.2.2.2, 3.3.3.3.
Installing Mod_Cloudflare
If you would like to install this module on your server, please follow the instructions listed below. We are including the steps for a cPanel/Linux environment using EasyApache3 and EasyApache4.
Note: You will need to run command-line commands in SSH in order to install this module.
EasyApache3 (Legacy)
For an EasyApache3 environment, please run the following commands:
wget https://raw.githubusercontent.com/Cloudflare/mod_Cloudflare/master/EasyApache/installer.sh
bash installer.sh
Command-Line breakdown: These commands will download the official installer and execute that file for installation.
Next, you can use EasyApache3, choose to customize your profile, then, on the ‘Short Options List’ screen, checkbox the ‘Mod Cloudflare’ feature, and click ‘Save and Build’.
EasyApache4
For an EasyApache4 environment, please run these commands:
bash <(curl -s https://raw.githubusercontent.com/Cloudflare/mod_Cloudflare/master/EasyApache/installer.sh)
wget https://raw.githubusercontent.com/Cloudflare/mod_Cloudflare/master/mod_Cloudflare.c
yum install ea-apache24-devel
apxs -a -i -c mod_Cloudflare.c
rm /etc/apache2/conf.modules.d/mod_Cloudflare.conf
service httpd restart
Command-Line Breakdown: The first command will download the Mod_Cloudflare source, then using the ea-apache24-devel you can have your system compile the source for your web server to utilize. The next command will remove the new configuration file in favor of the file created during the first command. Finally, the last command will restart the apache service thereby loading the new module.
You can then verify that the module is running by using this command:
httpd -M | grep Cloudflare
This command will generate a dump of running modules and the “grep” command will search for the keyword “Cloudflare” specifically and output a result similar to the screenshot below: