Hardening
The phrase “hardening” refers to implementing security features and code to secure the application against common attack methods. For most WordPress applications, brute force attacks are the most common attack method that is leveraged against the site. There are many more inventive ways to exploit your application, we will discuss these methods and how to defend against them.
Administrator Dashboard Lockdown
To combat these attempts, we recommend configuring a rule in your .htaccess file to restrict access to the administrator dashboard and exploitive files like admin-ajax.php or xmlrpc.php which can very negatively affect your sites and the server environment when abused.
To protect your WordPress site in WCP, please follow the steps below:
-
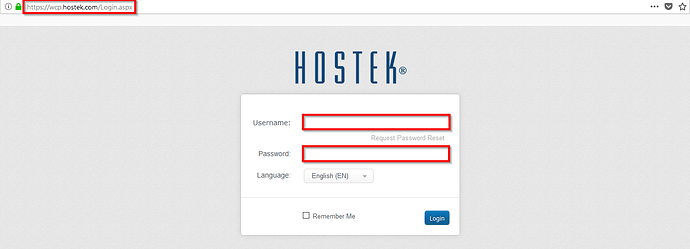
Login to your WCP control panel.
-
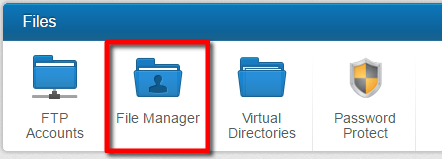
Next, navigate to the file manager and login to your file structure.
-
Now, either edit or create a “.htaccess” file in the /wwwroot/ directory (or webroot for a subdomain) and add the following code to the file.
RewriteEngine On RewriteCond %{REQUEST_URI} ^(.*)?xmlrpc\.php(.*)$ [OR] RewriteCond %{REQUEST_URI} ^(.*)?wp-login\.php(.*)$ [OR] RewriteCond %{REQUEST_URI} ^(.*)?admin-ajax\.php(.*)$ [OR] RewriteCond %{REQUEST_URI} ^(.*)?wp-admin$ RewriteCond %{REMOTE_ADDR} !^123\.123\.123\.123$ RewriteRule .* `http://0.0.0.0/Please_check_your_htaccess_file_or_contact_your_hosting_provider_for_assistance` [R=301]Note: You will need to replace the !^123.123.123.123$ with your IP address. You can find your public facing IP address using the following tool: https://hostek.com/ip
To protect your WordPress site in cPanel, Please follow the steps below:
-
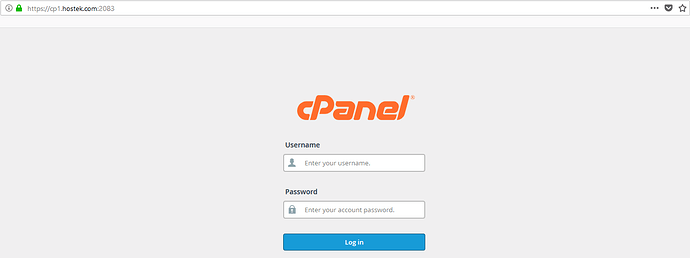
Login to your cPanel Account.
-
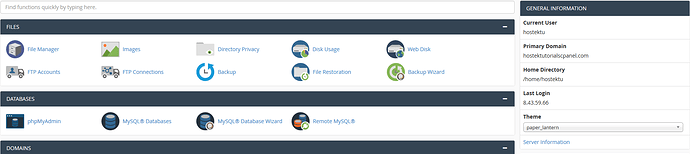
Next, navigate to the File Manager and select it to access your file structure.
-
Now, either edit or create a .“htaccess” file in the public_html directory (or webroot for a subdomain) and add the following code to the file:
<FilesMatch 'wp-login|admin-ajax.php|wp-admin|xmlrpc.php'> RewriteEngine On RewriteCond %{REMOTE_ADDR} !123.123.123.123 RewriteRule .* http://0.0.0.0/Please_check_your_htaccess_file_or_contact_your_hosting_provider_for_assistance [R=301] </FilesMatch>Note: You will need to replace the !123.123.123.123 with your IP address. You can find your public facing IP address using the following tool: https://hostek.com/ip
Once your IP address has been added, you will now be able to access your WordPress administrator dashboard while access attempts from other IP addresses will be denied.
There are also other methods for maintain the WordPress site security. We have Listed a few of these options below:
Turn Off Error Reporting
When a plugin or theme experiences an error it will sometimes display an error message. Error messages can be used to determine the server path. With this information, your sites file structure could be extrapolated, presenting a potential security vulnerability.
The vulnerability can be easily addressed by adding the following PHP directives into your wp-config.php file, thereby disabling Error Reporting for your WordPress site.
error_reporting(0);
@ini_set(‘display_errors’, 0);
If there comes a time where you need to display the errors, you can enable them by removing the lines or changing the values to “1” from “0”.
Defending Against SQL Injections
Another method in which attackers will attempt to exploit your WordPress applications is to use a form or submission method that would allow a visitor to submit/POST information to your site. When these forms are not properly sanitized, they can end up accepting/“POSTing” malicious queries to your database. These types of attacks are called SQL-Injection Attacks.
To combat these kinds of attacks we recommend adding the following code to your .htaccess file to have the POST data “checked” to alleviate malicious queries.
Options +FollowSymLinks
RewriteEngine On
RewriteCond %{QUERY_STRING} (<|%3C).*script.*(>|%3E) [NC,OR]
RewriteCond %{QUERY_STRING} GLOBALS(=|[|%[0-9A-Z]{0,2}) [OR]
RewriteCond %{QUERY_STRING} _REQUEST(=|[|%[0-9A-Z]{0,2})
RewriteRule ^(.*)$ index.php [F,L]
Limit User Access
Giving permission to only what is needed is a golden rule of site security. To this end, We recommend that you limit the number of users who will have access to your administrator dashboard. For the users that are generated, if they are non-admin users, limit the user access to the administrator tools.
Implementing these rules may seem tedious and somewhat of a hassle but in the long run, it is a much safer habit toward ensuring that your site remains safe from malicious intent.
For more information regarding WordPress Roles, please see the following link:
Reducing The Number Of Plugins
The WordPress Core installation is rather secure out of the box. Each release goes through rigorous testing to ensure maximum security. However, plugins may not have any security testing, or may not have been updated for years. Reducing the number of plugins will help to harden the security of your site. We also recommend that if you have plugins that have been installed in the application that you are no longer using, be sure to completely remove the plugin so that it will not be exploited later on. A plugin doesn’t have to be “active” to be exploited. The same goes for your themes. This is not to say that plugins are inherently insecure, but proper research and regular updating of plugins used will help to minimize your exposure to security threats.
Setting Secure File Permissions
Setting the correct file permissions for your hosting environment is an important step towards ensuring site safety. With regard to our hosting environments you will want to configure the following file permissions:
- Linux/Apache: Files: 644 Directories: 755
- Windows/IIS: Apply full access (Read, Write, Modify) for IUSR and IIS_IUSRS
For more information regarding WordPress File Permissions, in the Linux environment, please see the following link:
Avoid Using Pirated or "Free" Premium Plugins
A large portion of “Free” or pirated premium plugins may contain malicious code. These are plugins that would normally cost money but are available for download from less reputable sites. Installing these kinds of plugins may compromise your site by including malicious code or by being out of date. If you are purchasing a plugin, ensure that the site you are buying it from is the official source for the plugin.
There are many more ways to implement a more secure application. A fantastic resource for finding answers to your security woes can be found in the link below. This webpage covers a much larger range of security-related issues and provides guides and information regarding implementation:
Alternative Options To Recover Your Site
Sometimes an intrusion can leave your site so impaired that the best option moving forward is to re-upload or rebuild the site. Here are few options that can help you in that endeavor.
Paid Site Recovery
If your site is unable to be recovered by standard methods, using a paid service may be an option to consider. There are several companies that offer WordPress recovery options. One option that we have found to be highly reputable is Sucuri:
Clean Backups To Restore Your Site
A strong local backup policy is another insurance policy for your site. Keeping local backups of your site files and databases in an unexposed location will allow you to have a starting place if your site is unrecoverable. However, please note, backups cannot always be trusted especially if they are backups of a live site, as opposed to pushing changes to a dev site first and backing that up before pushing to your live site.
Malicious code can stay hidden for days, weeks, or even months before releasing its payload. Keep this in mind if restoring your site from a backup.